Written by Teddy Kyung Lee | CTO | ICTK
1. CBDC is different from Cryptocurrency
CBDC (Central Bank Digital Currency) is a digital currency issued and controlled by Central bank. It is “paperless” fiat money in digital form. The CBDC is not the same as Cryptocurrency. They are both digital currencies, but not quite the same. Rather, the primary philosophical foci of two currencies show fundamental conflicts.
The cryptocurrencies like Bitcoin were born to avoid governmental controls on monetary transactions. The transactions are recorded in distributed ledger secured by blockchain technology. Under the “decentralized” ledger structure, no governmental institution like the Central bank needs to be involved. There is no national boundary in money transfer and so no custom taxation is involved with the cryptocurrencies. When the first time the Bitcoins brought attention to the public in 2017, thanks to the price surge in trading, most of the countries expressed concerns and were busy announcing regulations on cryptocurrency trading. Taxes are imposed on the profits generated by cryptocurrency trading, which is one of the efforts by governments to bring cryptocurrencies to the institutional system. It is obvious that the strong surge in Bitcoin value triggered the CBDC’s debut, partly due to the growing concerns raised by governments about cryptocurrencies.
Thus, we can see two philosophical conflicts running opposite directions from each other: one trying to escape from governmental controls and the other trying to confine things within a scope. As depicted in Figure 1, the ledger structure of cryptocurrencies can be modeled as (a) distributed structure (or decentralized structure), while the CBDC ledger system can be modeled as (b) centralized structure [1]. Note that the recent trend of the CBDC ledger model is not just a strictly “fully” centralized one but also shows partial adoption of the distributed ledger technology (DLT) into their structure, resulting in a “semi-centralized” structure similar to the two-tiered system in Figure 2. There are many debates on which model will eventually survive.
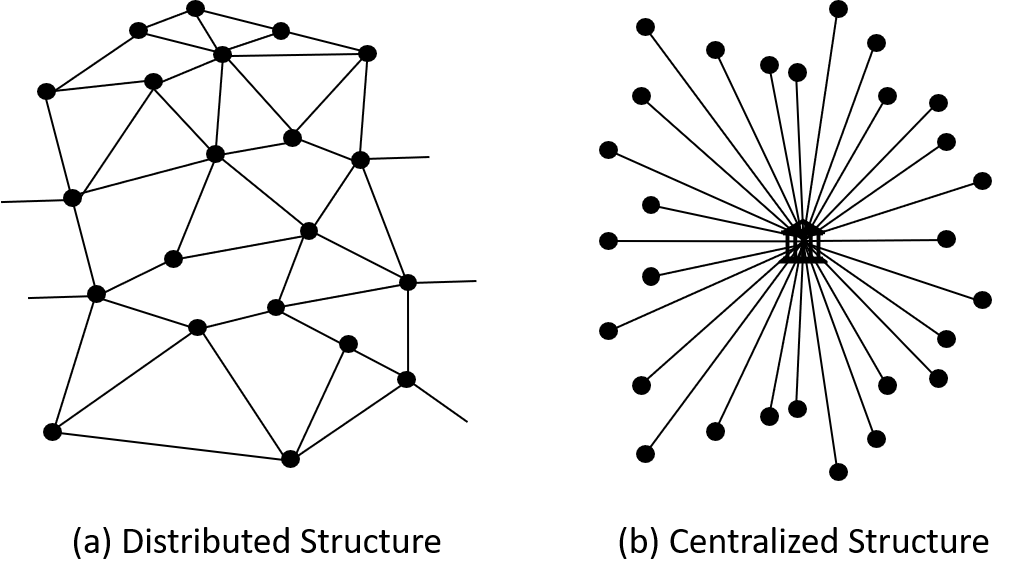
Figure 1. Ledger structure model of Cryptocurrency (a) vs CBDC (b)
Many countries perform research on CBDCs at this moment. The Bank for International Settlements (BIS) reported in the BIS 2021 paper that the vast majority (86%) of Central banks worldwide are exploring the benefits and drawbacks of CBDCs even amid the Covid-19 pandemic in 2020. The number of participating Central banks increases in year-to-year reports. A few participating countries already issued “preliminary” CBDCs including the DCEP from China, the E-Krona from Sweden, the Sand Dollar from the Bahamas, and the DXCD from Eastern Caribbean Currency Union, among which it is reported that the Bahamas launched the first “live” general purpose of CBDC, the Sand Dollar, for its residents in October 2020 (source: the BIS report 2021[2]).
It seems more countries will be joining the Bahamas in the next few years. According to the media, China is aiming to release the DCEP to the public before the start of the 2022 Winter Olympic Games in Beijing. The US Central bank, the Federal Reserve, seems to warm up performing research and experiments on how to proceed on a potential “digital dollar” project. The “Digital Euro” also emerges with experimental prototypes to decide “go” or “no go”. Norway’s Central bank recently announced that it is ready to start testing technical solutions for CBDCs over the next two years.
CBDCs provide efficiency and safety in the payment system such as 24/7 instant and secure settlement of fund transfer for end users. Introducing CBDCs will make significant changes in financial market structure and dynamics which will, on the other hand, lead to a role shrinking of conventional financial institutions. This will make financial industry executives nervous since revenue loss is foreseen. This is one of the reasons that countries with bigger economic scale lag pioneer countries in the CBDC progress.
2. Architectural consideration of CBDC system
Most CBDC projects including China’s DCEP, Sweden’s E-Krona, Bahama’s Sand Dollar, and Digital Euro use a two-tiered operating structure in their prototypes as shown in Figure 2. The Central banks issue CBDCs to commercial banks and the commercial banks then distribute them to individual users and business units by setting up and managing digital wallets. Government Authorities perform the anti-money laundering and counter-financing of terrorism (AML/CFT) checks upon requests. Commercial banks or financial institutions manage user’s interactions such as user authentication, device set up and authentication, user account settings, and payment processes. They can also freeze and seize user accounts including transaction reversals when necessary.
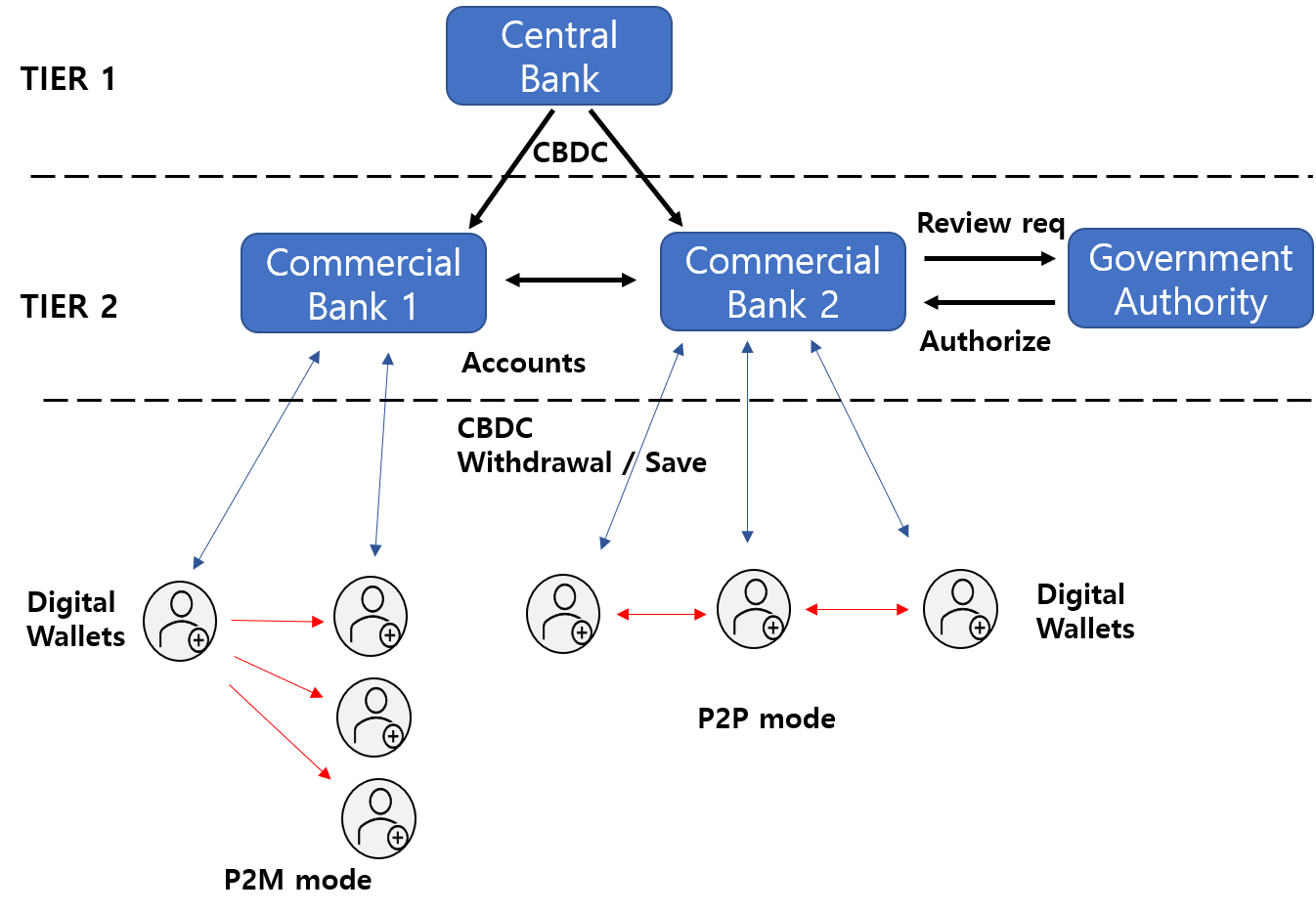
Figure 2. Two-Tiered Operating Structure in CBDC system
Digital wallets are the interface for users to send or receive payments of CBDCs to other users or business units. The CBDC systems can adopt digital wallets which can support P2P (Peer-to-Peer) mode and P2M (Peer-to-Multi peer) mode at the user end. The P2P and P2M modes would guarantee the security of transfer as well as the privacy of users in either online or offline transactions.
Even if fully decentralized blockchain technology is studied for CBDC applications, it does not seem that it will be adopted by CBDC because the fully open and transparent feature of the blockchain may not be able to comply with the laws and regulations enforced by governments. Instead of using the fully open and transparent feature of the blockchain, the CBDC will likely take the form of DLT (Distributed Ledger Technology) implemented in a private network, which makes more sense from a controllability point of view by Central banks. The private network–based DLT is also called “permissioned” DLT or “private” DLT.
The good side in CBDC systems
Compared to the conventional financial system, the most prominent benefits of living with CBDCs from a user’s point of view are related to the improved efficiencies in payment system, especially in the international cross border payment system, which is the faster settlement time of transactions and lowering the associated monetary cost. The peer-to-peer payment using digital wallets may not require the upfront services from intermediary banks for sending and receiving funds as we do today, so people would enjoy cheaper operational costs. Lack of paper currency can save tremendous operating costs such as maintaining ATM centers and physical vaults for cash storages, printing paper currency, and distributing the paper currency to commercial banks, etc.
Governments would expect the CBDCs to bring more benefits to their financial management system. As CBDC systems may attract more people to use and all issued tokens can be traceable, the system can open a broader positive tax base for governments. At the same time, the system can help governments to reduce illegal tax avoidance. CBDCs could potentially help developing countries to improve financial inclusion for their people who currently do not have access to the banking system.
The downside in CBDC systems
One of the main goals of the CBDC system is to protect users from malicious attacks and to guarantee the anonymity of their monetary transactions. Identity privacy and transaction anonymity are two types of anonymity expected from cash transactions, which are not trivial to keep in the CBDC system. When the “decentralized” DLT structure of blockchain technology is adopted in the CBDC system, the details of transaction history can be revealed with known ledger addresses, which is not desirable from a cash user’s point of view. How to protect privacy is one of the main research items in the CBDC area.
3. Digital Wallets for CBDCs
A digital wallet is a software program or a hardware device that can store digital assets, through which users can access the assets for financial transactions such as viewing, trading, sending, receiving, and exchanging the assets which are supported by underlying functions like managing keys and addresses, tracking balances, and creating and signing transactions. The wallets protect digital assets by securely storing digital keys and generating wallet addresses for further external transactions. The digital wallets mainly refer to the ones for cryptocurrencies like Bitcoins and Ethereums, or money-transfer applications like Venmo or Alipay. How about CBDC wallets? What are the special features of CBDC wallets?
CBDC wallet as a bank agent: A wallet for CBDC has no standard architecture and yet to be defined. CBDC wallet is essentially a small size of bank inside a pocket or a handbag in the form of a credit card, a token type, or just a software application in a mobile phone. As people accept CBDCs as their standard payment method, the activities with CBDC wallets gradually replace the traditional banking services such as saving, withdrawal, payment, money transfer, and loaning service since a device at hand will take care of the banking needs that would otherwise have been done with bank agent’s help in offline. The CBDC wallets are then expected to provide the following functions for secure monetary transactions.
- User Authentication: CBDC wallets must authenticate the user’s identity for device access. It can be done by a simple PIN, password, or by biometric authentication methods. The FIDO (Fast Identity Online) standard can be also used for user authentication purposes in various types of devices.
- Transaction Authentication: sending or receiving money using CBDC wallets. The wallets must ensure that the target transactions are issued authentically by the user who is authorized to access them. Security breaches usually occur during the transaction. The security requirements are discussed later in the section below.
- User Interface providing users the information regarding the transaction
- A Balance between Privacy and Transparency: Not easy to protect user’s full privacy like in cash due to the traceability nature of CBDC. The recent trend shows a mix of those two that CBDC systems provide a certain level of privacy to users while also providing visibility or transparency to government authorities and law enforcement.
CBDC wallet as a self-sovereign identity: CBDC wallets also serve as the self-sovereign identity for people. Users can collect attestations from participating institutions such as government, schools, hospitals, and banks about users themselves, and store them in the wallet securely. The users can later use the attestations selectively when identity proof is required. One of the self-sovereign identity features is to let people actively “control” which attributes in their identity to reveal and to whom to reveal rather than passively expose everything as we might do it today. Adopting the self-sovereign identity features into the CBDC ecosystem is not trivial due to the difference in underlying data structures, but it would bring a significant boost up in CBDC user experiences.
4. Operational Use Models of CBDC Wallet Devices
Under a two-tiered system, the proposed operational use models of CBDC wallets are summarized in table 1.
Table 1. Proposed operational use models of CBDC wallets
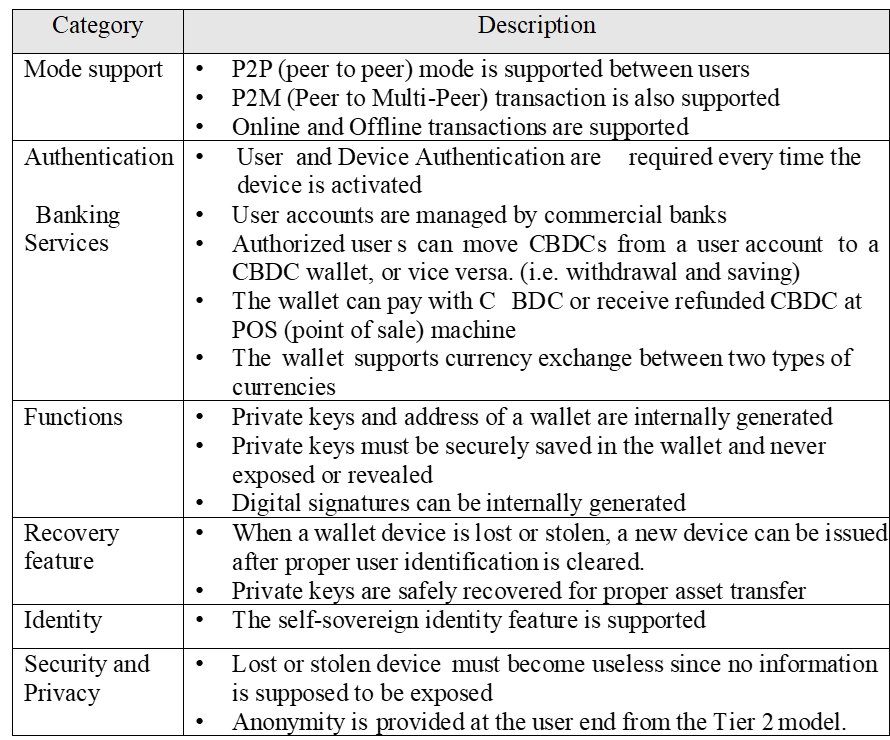
Offline mode support: The offline payment support in the CBDC system would be the most beneficial feature for end–users when it comes to anonymity. After the Central bank issues CBDCs with serial numbers assigned to them, the CBDCs in offline transactions are not to be tracked to protect the privacy of the transaction. The CBDCs are authenticated with Central bank–issued certificates and wallet private keys before committing the money exchange in P2P or P2M mode. The offline transaction would mean a “cash-like” exchange among individual wallets. This is quite a challenging task to achieve under the CBDC context because protecting privacy may imply giving up tracing which is a conflicting concept with transaction safety point of view. The offline transaction must be free from the security concerns mentioned in the later section “security weakness of hardware wallets” such as double spending, firmware attacks, and device tampering issues.
5. Root of Trust
What is the “Root of Trust (RoT)”? Why is it important for CBDC wallets?
The Root of Trust is a set of core functional elements in a hardware and software module that can be trusted and cannot be altered during the lifetime of the product. It is something that computer operating systems can rely on all the time. Something that cannot be copied or cloned. The silicon inborn unique identity embedded with the Via PUF technology (see section 7 for more details) is the Root of Trust, on top of which an ultimate trust can be built.
Since a CBDC wallet must protect its private keys from hacking attempts, the wallet should be built based on the RoT. Any hacking attempts to steal the secret information would be denied by the silicon inborn Root of Trust.
6. Hardware Wallets for CBDCs
A software wallet is an application program in mobile devices or personal computers. What about people without a mobile device or a PC? How would they make payments using CBDCs? A hardware wallet in a smart card type or a dongle type would be the solution for them as shown in Figure 4. The reason is not just because we need to cover non–mobile users, but because software alone is not secure enough against hacking attacks.
Key Management System in CBDC Wallets
(1) Key protection in PUF CBDC wallets
Private keys of CBDC wallet must remain secret all the time within the wallet, and never leave the device. A software wallet or hot wallet with secret information could be an easy target for malicious attackers. Once it is hacked and the private keys are stolen, the funds in the wallet may also be stolen permanently. Using a hardware wallet or a cold wallet can substantially boost up the level of security. However, even a hardware wallet could be exposed to security issues such as firmware modification or counterfeiting attacks in the supply chain. Injecting malware into the hardware device could end up revealing private keys to malicious attackers. The attacks can be done by external hackers or by insiders with malicious intentions. We propose the PUF (Physically Unclonable Function) based Root of Trust (RoT) technology for the ultimate solution protecting private keys securely within the device.
(2) Recovering private keys when lost
When a cold wallet device is lost or broken, we need to retrieve the asset by recovering the private key. The cryptocurrency wallets like Bitcoin wallets provide a key recovery mechanism that users need to write down a “mnemonic seed phrase” on paper when the wallet is initialized for the first time. The users need to save the seed phrase safely in a safe place, which can be used as a key recovery seed when necessary. However, when the phrase is lost somehow, the funds are lost forever. A recent study reported that about 3 or 4 million Bitcoins are lost forever because their private keys are lost. All the burden is on users to keep the information safe.
Is there any other way to recover it while minimizing the user’s burden? Multi-sig or multiple signature transactions can be the solution for it. A private key can be split into multiple shares using the Shamir’s secret sharing algorithm [3] where the shares can be used to reconstruct the original private key. The algorithm does not need all the shares to reconstruct the key but only a minimum number of shares are required which is called the “threshold” number.
Unlike the permissionless cryptocurrencies, however, the CBDC system maintains controls on digital money. In this paper, we propose to split a private key into 3 shares in the CBDC system and save 3 shares to 3 different entities: one for the owner of the wallet, the second one for the commercial bank where the user’s account is created, and the last one for a trusted third party running by government authority. When a CBDC asset needs to be recovered, the user needs to prove his/her identity to the trusted third party and the commercial bank for reconstructing the original private key. Dealing with banks and government authority may not be ideal for individual users, but the security concern is not small to overlook. The details of the recovery architecture can be developed to enhance the user experience.
Security Weakness of Hardware Wallets
Firmware issue: Hardware wallets may not be free from security issues due to the attacks targeting device firmware including firmware counterfeiting and the MITM (man-in-the-middle) attacks. If device firmware is compromised during device manufacturing or in shipping process, the digital asset in the impacted device could be stolen by attackers. A malware extracting the private key of a hardware wallet and rerouting payment address to the hacker’s address can be infiltrated into the original firmware resulting in sending the money to the hacker instead of the original intended recipient. Firmware protection must be guaranteed by CBDC wallet functions such as firmware encryption and authentication process as well as performing secure boot and secure firmware updates.
Double spending issue: Double spending means that the same single digital token can be spent more than once, which could break the entire CBDC system. The problem could be more serious when the transaction is in offline mode during which the Central bank has no immediate visibility. While the decentralized cryptocurrency system uses a consensus algorithm to address the issue, the CBDC system uses the controllability of the Central bank to revert any illegal transactions. However, the correction could be an expensive and unpleasant experience on the user side. Using a secure hardware wallet device at each user’s end can be the solution to address the double spending issue. The secure environment using secure devices like the Via PUF CBDC wallets, explained in the later section, can be used to enforce one–time spending on each digital token.
Device tampering issue: Malicious users who possess their own hardware device can attack the device physically extracting secure information from the device. The extracted information can be used for adversary attacks like spending the same token an unlimited number of times. This will break the whole CBDC system. That is why using the right secure hardware wallet is crucial. For example, the Via PUF CBDC wallet uses the unique inborn identity chip where the secret information such as the device’s private key is securely stored and never leaves the chip to the external world, not even to the malicious owner.
Wallets in PCs or mobile phones: Hardware wallets in PCs or in mobile phones are relying on software implementation in the hardware platform. The wallet private keys are usually stored in PC hard disk or SSD memory in mobile phones which can be an easy target for hackers due to their low security level. Malware can be installed unintentionally by the user’s permission. When a user tries to send money to a friend for example by copying and pasting the friend’s wallet address, the malware can replace the address in the clipboard with another one. Since the address is usually a long and complicated string, the user does not know the money is going out to somewhere unintended. Careless users can also be tricked into a phishing website or a cloud where they may reveal secret information such as a password or private keys.
Proposed solution in PCs or mobile phones: How do we protect the “naive” users from the attacks on PCs or mobile devices? We propose USIM/eSIM cards embedded with the Via PUF technology, the silicon inborn Root of Trust, to protect the user’s secret credentials in PCs or mobiles. A USB dongle type of hardware wallet could be an alternative solution as described in the “Via PUF Wallet” section below.
7. Introduction of the Via PUF Hardware Wallet
The Via PUF Technology
The Via PUF (Physically Unclonable Function) technology is based on “Via” or “Contact” formation during the standard CMOS fabrication process. The technology is the outcome of the reverse thinking process. Rather than meeting the design rules, it makes the sizes of Via or Contact smaller than the requirements in a controlled manner, resulting in the unpredictable or stochastic formation of Via or Contact where the 50% of randomness is achieved in a chip as shown in Figure 3. We use the property to establish the silicon “InbornID” PUF technology, where the “InbornID” means that the unique random number is self-generated within a chip, not injected [4]. The unique InbornID characteristic enables the Hardware Root of Trust (RoT) technology in a silicon chip. What are the advantages of using the Via PUF as a Root of Trust in CBDC wallet implementation? The details are described in Table 2. The Via PUF characteristics are the core factors for satisfying the requirements of CBDC wallets as shown in Table 1. The security SoC (System on chip) products based on the Via PUF technology are currently in mass production. More details can be found in [5].
Table 2. Technology advantages of the Via PUF
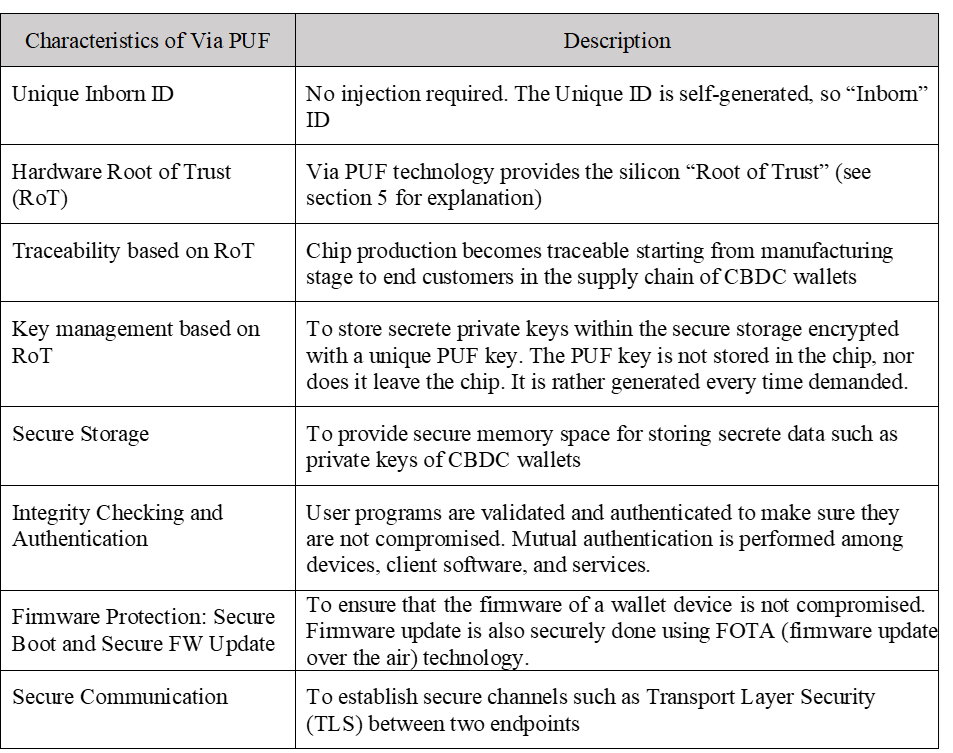
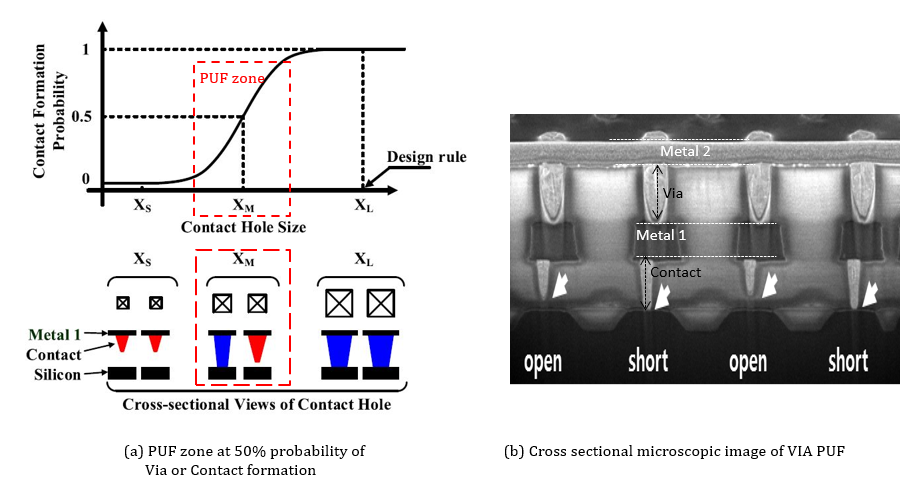
Figure 3. Via PUF Technology
The technical discussions regarding the Via PUF technology can be found in [6]. The international standardization efforts on security requirements and test methods for PUF for generating non-stored cryptographic parameters are currently actively ongoing as of today under ISO/IEC 20897-1. As the standardization process is being finalized, we can expect that the PUF technology becomes more scalable and its market demands grow exponentially.
Via PUF Hardware Wallet
A hardware wallet for CBDC applications can be built in many ways, where applying the Root of Trust technology is crucial to protect digital assets. We propose the Via PUF based hardware wallets whose variations are in a USB dongle type or a smartcard type for standalone applications (Figure 4), and a USIM/eSIM card type for mobile applications.
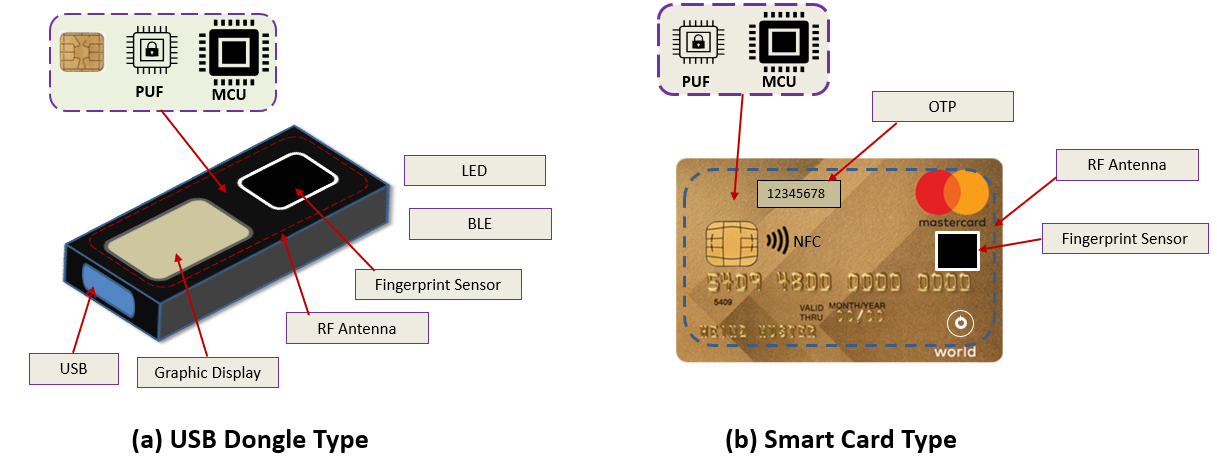
Figure 4. Types of Hardware Wallet for CBDCs
(1) Why Via PUF technology?
The Via PUF provides an unbreakable security origin for the hardware Root of Trust (RoT) technology. The CBDC wallets need to use the hardware RoT for their own security protection. Since the private keys of CBDC wallets are stored in secure memory encrypted by an internally generated PUF key, and the PUF key is never stored in the chip but generated every time it is called, it is practically impossible to steal the key by hacking. Since all the security–related functions are executed within the security boundary, no sensitive information is exposed to the external world.
(2) User authentication with USIM/eSIM PUF
The Via PUF CBDC wallets use biometric fingerprint sensing technology for user authentication. The fingerprint templates are stored in the secure storage of the USM/eSIM PUF chip and never leave the chip. Only the matching results are sent to MCU for display. The authentication by HMAC algorithm or by certificates can also be used in the USM/eSIM PUF device. A PIN–based authentication method could be provided in case the fingerprint unlocking is not desired at the user end.
The FIDO (Fast Identity Online) technology could be the alternative option for user authentication. The wallet public key is pre-registered in the FIDO server at the “Relying” party and the user fingerprint is locally registered and authenticated. The technology allows users to access the device with their fingerprint credentials without typing ID and password. However, the wallet device should be connected online to use the technology.
(3) Secure wireless connectivity
The wallet device supports Bluetooth or NFC (Near Field Communication) short-range wireless communication with built-in PUF based security functions such as device authentication, secure boot, data integrity checking, secure firmware update, and secure access to the Tier-2 servers in the CBDC system. Using secure wireless connectivity, the CBDC wallets can communicate with other CBDC wallets for monetary transactions which include P2P mode and P2M mode.
(4) User-friendly interface and experience (UI/UX)
When sending a cryptocurrency asset like a Bitcoin to an incorrect address, it is impossible to retrieve the asset back. On the other hand, since the government authority or the commercial banks in the two-tiered CBDC system control the asset transactions, the misplaced CBDCs can be retrieved. The downside is that the government involved backing up process usually takes time which would be an undesirable experience for users. The better user interface design, the easier system acceptance by users and so the more enhanced system security it derives to. The Via PUF CBDC wallets provide a user-friendly interface helping to ensure the information user provided is indeed correct.
(5) Key recovery service
As we proposed in the previous section, the private key is split into 3 shares and save the shares to 3 different entities each: one at the owner’s wallet, the second one at a commercial bank, and the third one at the government authority. When the shares are saved in each entity, they are encrypted for safety with a Via PUF chip.
8. Conclusion
The various aspects of the CBDC system are discussed. Unlike the decentralized ledger structure in the cryptocurrency system, most of the existing CBDC prototypes adopt a “semi-centralized” ledger system which allows partial or controllable anonymous privacy for users while the controllability of the Central bank is maintained. The security of the CBDCs is crucial for the entire system. We explained the Via PUF CBDC wallets powered by the “silicon inborn unique identity” technology bring the ultimate security features to the CBDC system.
References
[1] Paul Baran, “On Distributed Communications: Introduction to Distributed Communications Networks”, Memorandum RM-3420-PR, August 1964.
[2] BIS Papers, No 115, “Multi-CBDC arrangements and the future of cross-border payments”, https://www.bis.org/publ/bppdf/bispap115.pdf, March 19, 2021
[3] “Shamir’s Secret Sharing”, https://en.wikipedia.org/wiki/Shamir%27s_Secret_Sharing
[4] Teddy Kyung Lee, “Via PUF Technology as a Root of Trust in IoT Supply Chain”, Global Semiconductor Alliance Forum Article, May 8, 2020.
[5] www.ictk-puf.com/chips
[6] D. J. Jeon, et al., “A Physical Unclonable Function with Bit Error Rate < 2.3×10-8 based on Contact Formation Probability without Error Correction Code,” IEEE J. Solid-State Circuits, vol. 55, No. 3, pp. 805-816, March 2020.
___________________________________________
 About Teddy Kyung Lee | ktlee@ictk.com | www.ictk.com
About Teddy Kyung Lee | ktlee@ictk.com | www.ictk.com
Teddy Kyung Lee is an IoT security professional working on bringing security features to network components such as Serial to Ethernet, LoRa network, Smart IoT sensors, Industrial IoT, and FIDO applications. He is recently interested in Hardware Root of Trust solution using Physical Unclonable Function (PUF) technology extended from his career background in hardware SoC design.
Teddy received a Ph.D. and M.S. degrees in Electrical Engineering from the University of Texas at Austin, and a B.S. degree in Electronics Engineering from Seoul National University, Seoul, South Korea. He worked at IBM Research Lab, Austin, TX, and Sun Microsystems, Sunnyvale, CA, as a circuit designer in microprocessor designs. Thereafter he worked at Juniper Networks, Sunnyvale, CA, and then Altera Corporation, San Jose, CA as a methodology leader. Scouted as an overseas brain by the Korean government, he worked in IoT security and FIDO applications.