Written by Teddy Kyung Lee | CSO | ICTK Holdings
1. Introduction
Recently the world-first product of PUF-USIM card is commercially debuted by the telecom giant, LG Uplus from Korea, and the security solution company, ICTK Holdings [1] (Figure 1). The PUF-USIM is the perfect combination of two technologies between user-friendly USIM functions and the strong security features added by the Via PUF (Physical Unclonable Function) technology, resulting in the birth of a “robust PUF secure element”.
Figure 1. The world first PUF-USIM card
Telecom companies seem to be expanding their businesses beyond the traditional communication area and strategically advancing to the “Metaverse” platform business. The metaverse refers to a persistent online 3D virtual universe where users can interact and stay connected to work, play, or socialize. They can even buy and sell digital assets in the form of blockchain-based NFTs (Non-Fungible Tokens). Metaverse and NFTs are a new paradigm shift that is “crossing the chasm [2]” in business where endless opportunities exist since everything in the real world can be duplicated in the virtual universe. The telecom giants in Korea are putting efforts into being leaders in the metaverse business requiring them to guarantee cyber security in the online platform, which is why they are incorporating the strong security provided by the PUF-USIM into their products.
The PUF is the silicon inborn Root of Trust (RoT) function that provides end-to-end security in the IoT supply chain as well as in all types of telecommunications. The USIM is known to be secure to store subscribers’ personal information. However, it has been discovered that USIM chips are exposed to various types of hacking attacks such as SIM cloning and swapping, and man-in-the-middle (MITM) attacks. Can the PUF technology fill the security gap in the USIM applications and make them even stronger?
This article introduces the industry’s first PUF-USIM product and explains how the PUF technology can enhance the security feature of USIM applications. The article also talks about what benefits and synergy effects we can obtain from the combination of two elements. We also cover a few potential applications that can be built using the PUF-USIM product which include the recent hot topic of metaverse platform and NFT applications.
We will talk about the fundamentals of the Via PUF technology, and then about a few aspects of USIM applications. The benefits of combining two elements will be explained. Finally, the applications of the PUF-USIM products will be discussed.
2. PUF as a Device Security Service
The PUF is the core technology used in the Hardware Root of Trust (RoT) function which is the fundamental core element of security. The RoT is a set of core functional elements that the computer operating system relies on as a trusted service that cannot be modified during the lifetime of the product. The recent trend in the industry is to include the RoT function within the standard design flow and manufacturing process as an IP. This implies that the RoT becomes part of all the products and provides the core technology for traceability in the trusted supply chain. The unique inborn identity generated internally within a PUF chip is used to establish trusts along the supply chain. It can be viewed as “PUF as a Device Security Service” since the traceability and security aspects in the supply chain bring value to customers who can then see the integrity of original products. The device security service can be applied to all industrial sectors including the IoT industry.
Via PUF technology
We introduce the Via PUF technology as part of the security service. The Via PUF is based on a “Via” or “Contact” formation during the standard CMOS fabrication process. Rather than meeting the IC design rules, the sizes of Via or Contact are designed to be smaller than the requirements in a controlled manner, resulting in the unpredictable or stochastic formation of Vias or Contacts as shown in Figure 2. Note that the PUF Vias or Contacts are spread out in the entire chip area and are indistinguishable from normal logic, which is the unique characteristic available only with the Via PUF technology.
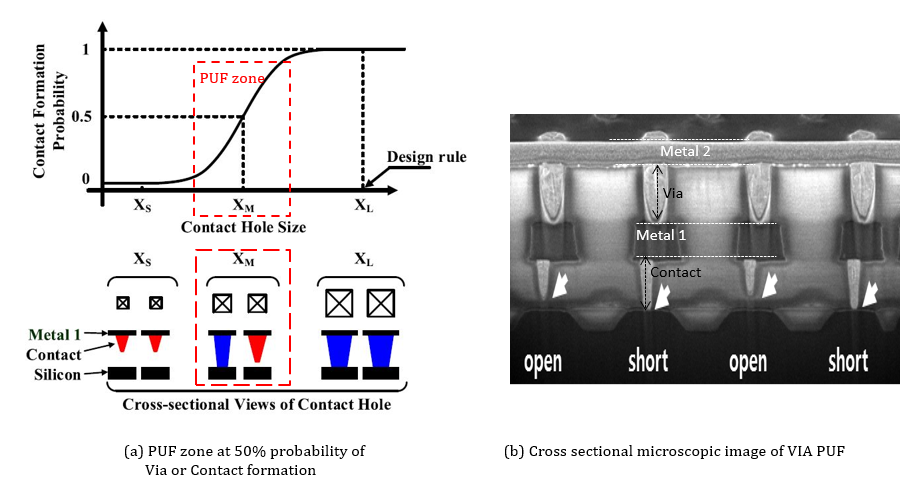
Figure 2. Via PUF technology (source: D. Jeon, et al, JSSC, 2020)
The Via PUF based Inborn Identity and the PUF key are the core components that establish the Hardware Root of Trust in a silicon chip providing essential security functions in the security service area.
PUF Standardization and its Requirements
The international standardization efforts on security requirements and test methods for using a PUF to generate non-stored cryptographic parameters are ongoing and as of today are defined under ISO/IEC 20897-1/2. Part 1 of the standard defines the security requirements of a PUF which are: steadiness, randomness, uniqueness, tamper resistance, and mathematical and physical unclonability. Part 2 defines the test and evaluation methods which consist of design inspection and comparison of PUF performance against the specified thresholds. The Via PUF satisfies the requirements as shown in the technical discussions presented in [3][4].
3. The PUF-USIM module
(1) What does USIM stand for?
The SIM (Subscriber Identity Module) cards mounted on phones are used for identifying and authenticating subscribers on mobile networks. The cards also store the subscriber’s personal information such as contact numbers, short message services (SMS), and secure information such as the identification numbers and the security key file that are used for registering devices on the network.
The physical format of SIM cards or UICC (Universal Integrated Circuit Card) has been shrunk over the years as shown in Figure 3. The original SIM, the Mini-SIM, the Micro-SIM, and the Nano-SIM cards are all detachable UICC that can be removed from one device and inserted into a different device. The latest trend in the format is, however, to adopt the eSIM (embedded SIM) format. Unlike its predecessors, the programmable eSIM is not detachable but directly embedded into a device.
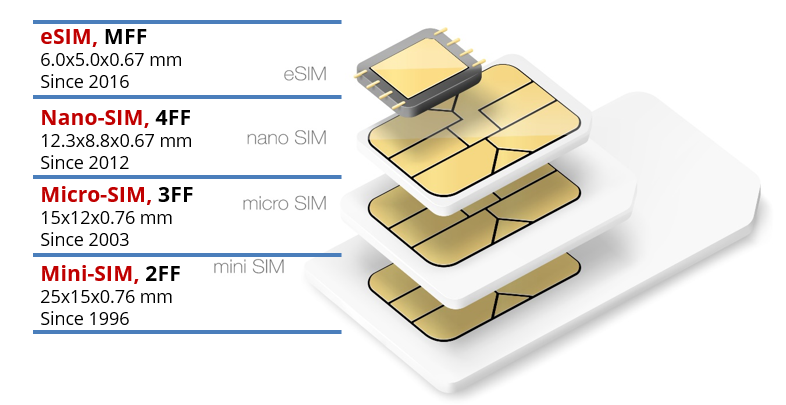
Figure 3. SIM card formats over the years
As opposed to the concept of the “embedded” eSIM, the detachable SIM cards are usually called “USIM” in several countries including South Korea. This conventional naming causes a bit of confusion with the USIM (Universal Subscriber Identity Module) which refers to the SIM applications running on a UICC device under the UMTS (Universal Mobile Telecommunications System) network. The UMTS is a third-generation mobile cellular system for networks based on the GSM standard. Note that the USIM in this article is used for “detachable” UICC smart cards as compared to the “embedded” SIM cards (i.e., eSIM).
The UICC smart cards or SIM cards consist of CPU, ROM, SRAM, non-volatile memory like EEPROM, and the ISO/IEC 7816 interface. The USIM cards are intended to securely store the user and the network information within the device. However, USIM alone may expose weak points from the security point of view as we discuss in the later section. Table 1 shows a typical example of what is stored in the USIM storage. The integrated circuit card identifier (ICCID), the international mobile subscriber identity (IMSI), and the local area identity (LAI) are the identifiers of a USIM card.
Table 1. A typical example of USIM storage contents
| Identification and Env files | ICCID, IMSI, LAI, Network Provider, Language, Location Info |
| Service files | Emergency call number, Call numbers (ADN, FDN, SDN), Service Network |
| Security authentication files | Authentication Key, PIN/Unlock PIN, Error Count, Data integrity Key, Encryption Key |
The authentication key must be securely protected from unauthorized access since they are used to authenticate and identify subscribers on the network. If the user and the network information including the key are revealed, they can be used for malicious attacks such as SIM swapping, SIM hijacking, or SIM cloning.
(2) Vulnerabilities of USIM
SIM swapping or SIM hijacking attack is when a scammer convinces a subscriber’s network carrier to switch the original phone number over to a different SIM card that the scammer owns. The text-based or call-based two-factor authentication checks are diverted to the scammer’s new SIM card resulting in the original subscriber’s sensitive information including passwords for bank access being hijacked. This attack requires a human intervention of convincing carrier operators using the victim’s personal information. Obtaining the subscriber’s personal information is quite easy these days by following the victim’s SNS activities. A hardware authentication device employing the PUF technology can prevent this type of attack.
SIM cloning attack is to duplicate a SIM card using smart card copying software and a card reader. The secret information such as the subscriber’s identification number and the authentication key is pulled out of the victim card and copied onto a new faked SIM card. This is a more serious problem from a SIM security perspective since it works only through technical manipulation without any human intervention. The PUF technology can also stop the attack because when a secure element based on PUF technology is used, no secret information can be extracted from the original device.
Man-in-the-middle attack using SIMtrace software and hardware can intercept the transmitting APDU (Application Protocol Data Unit) packet between a SIM card and a mobile device. The eavesdropping attack can harvest sensitive data such as authentication key and AID (application ID) in the SIM card.
External key injection could be one of the weakest links in the existing SIM applications since the identification numbers and the authentication keys are injected into the SIM cards from external sources, which must be done in a secure environment to avoid potential hacking attacks. This is where the great advantages of PUF technology can be realized by utilizing the inborn identity and removing the burdensome injection process. PUF technology can fill the gap since it generates the secret authentication keys and the unique identification numbers internally within the chip using the inborn identity. They do not need to be stored in the memory space of the chip, because the same unique keys can be generated every time they are required. This feature makes the PUF technology strong against the attacks like SIM cloning and SIM swapping which try to reveal the secret authentication keys.
Key questions to ask:
We can ask several questions at this point: How can PUF technology be used for boosting up the security feature of SIM applications? What benefits can we get from the combination of two elements? Are there any commercial products available to address the problem?
(3) Benefits of combining USIM and PUF technology
Inborn keys vs Injected keys: “Inborn vs Inject” are two words that clearly show the difference between PUF-USIM chip and just USIM chip. The device secret keys described in Table 1 need to be “injected” in the conventional USIM cards during the manufacturing stage called the key provisioning process. The key provisioning must be done in a secure environment isolated from the external world which is quite costly to maintain. The PUF-USIM has no key provisioning process because the key is born internally. No need to inject it and no need to store it. This fact boosts the PUF-USIM up to the next level from the security perspective and contributes to a reduction in manufacturing and assembly costs. Embedding a PUF IP inside a chip is now an industry trend.
Unique key across the board: The PUF key is unique across the board which means each inborn key has a different value from the other. No same PUF key will be generated. This characteristic is practically hard to meet with the conventional USIM card where the keys need to be injected. Maintaining the injection keys to be all different across the board would increase the manufacturing and test cost significantly. This is another winning point of combining PUF and USIM.
Root of Trust to be added: By adding the PUF technology to USIM, the SIM applications can be built on top of Hardware Root of Trust. For example, the file creation and access would be done in a secure way in a PUF-USIM chip as depicted in Figure 4. When a file is created, it is encrypted with the PUF key before being saved in the storage. File access is granted only after authentication is verified.
Hardware Crypto Acceleration: A hardware cryptographic accelerator is also part of the RoT platform that the combined PUF-USIM utilizes. For example, the data transfer between USIM and phone applications can be encrypted for protecting the data from the man-in-the-middle attack.
Secure Storage: The strong protection of data with the PUF key is one of the main advantages over the original USIM card. The combination of PUF with USIM enables the protection of the secure information listed in Table 1 within the secure storage. For example, the private key of a digital CBDC wallet [5], or the biometric credentials such as subscriber’s fingerprint templates are saved locally in the PUF-USIM device. No data leakage is possible.
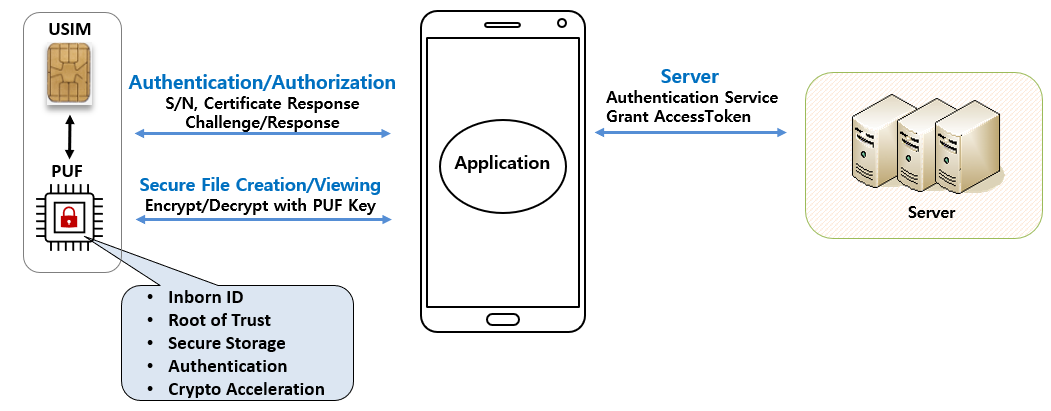 Figure 4. The benefits of the PUF-USIM combination
Figure 4. The benefits of the PUF-USIM combination
App-permission check and applet authentication: When an application program running on the phone tries to talk to a USIM card, the telephony service sends commands and data to the card framework through the radio interface layer (RIL) as shown in Figure 5. The application program accesses the USIM with an AID (application ID) which is a unique ID assigned by the network operator. When an unauthorized 3rd party application tries to access the USIM card with a faked AID, the permission check will block the access. However, it has been reported that the permission check can be easily bypassed with a minimum hacking effort. This is where we can apply the PUF-based authentication procedure to solve the vulnerability issue on the permission checks. The applets running at the card are also authenticated using the secure firmware update procedure which stops any unauthorized applets from executing in the card.
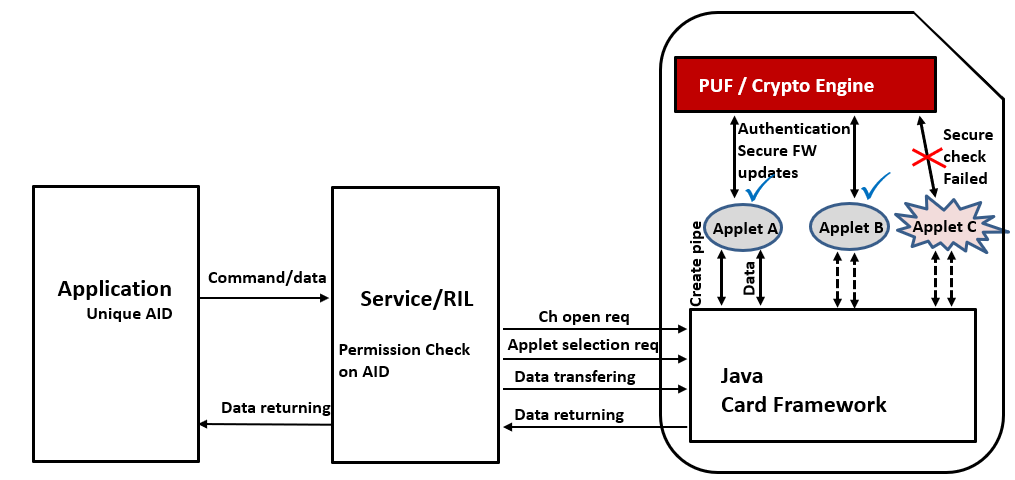 Figure 5. USIM communication data flow and applet authentication by PUF
Figure 5. USIM communication data flow and applet authentication by PUF
(4) Industry applications using PUF-USIM
Numerous applications can be considered using the PUF-USIM technology, among which include the recent hot topics of Metaverse and NFT platform applications. An NFT becomes a collectable digital asset by adding a unique signature to a digital work which can be an artwork, an image file, a song, a video, or any other digital format file. The NFT fuels the metaverse platforms since users in the metaverse can buy, sell, and trade NFTs, or send NFTs to anyone in the platform. Amid the pandemic fear and agony, people are getting more used to doing online activities than ever before, which implies that the metaverse experience gains momentum.
The transactions in the digital environment, however, bring huge challenges of protecting digital assets from hacking attacks such as identity theft and fraud. The NFT transactions such as trading, buying, or selling must be validated and the unique signature data needs to be verified. Keeping the security level high becomes the most important factor in building the metaverse platform.
We introduce the PUF-USIM based metaverse platform as a use-case of the product. The high-level architecture is shown in Figure 6. The metaverse platform and the mobile applications are built on the PUF-USIM based components. The secure key management system and the payment gateway are supported by the PUF based certification and authentication services. The marketplaces in the digital world also need to be built on the security functions for goods exchange.
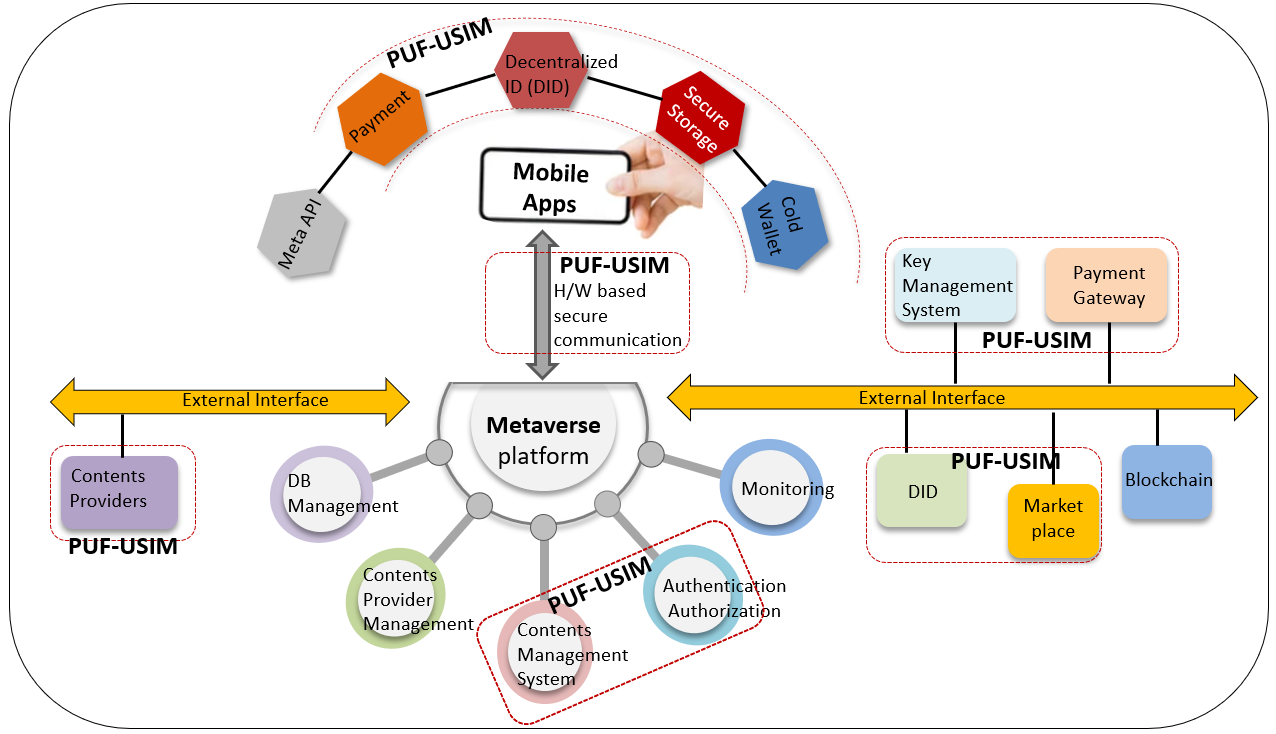 Figure 6. Metaverse platform powered by PUF-USIM
Figure 6. Metaverse platform powered by PUF-USIM
We can also bring the product to the areas like smart cities, smart factories, and smart homes where strong security services are required. The combined technology provides digital wallet functions in the service areas where digital access keys and user authentication services are required. For example, the financial and digital asset-related P2P services such as CBDC (Central Bank Digital Currency) wallet and NFT wallet are an upcoming trend in people’s daily lives where the security service provided by the PUF-USIM technology takes a crucial role.
(5) Conclusion
This article introduces the PUF-USIM technology, and the industry use cases delivered by the telecom giant, LG Uplus for the first time in the industry. The PUF technology can perfectly complement the vulnerability issue of the existing USIM cards. The hardware inborn identity and the secure storage feature of the Via PUF technology enable the Root of Trust function in the combined PUF-USIM product. People being forced to stay inside their homes during the pandemic era tend to visit the virtual digital world such as the metaverse platform where people buy and sell digital assets in the form of NFT. The importance of security is growing higher as more people flock into the virtual world. The PUF-USIM product provides confidence to users as fundamental components to build an end-to-end security system in the mobile world. It opens huge opportunities in many areas including the meta-verse and the NFT area.
Acknowledgments
The research in this article was supported by task 2021H1D3A2A02096391 under NTIS assignment #1711141235.
References
[1] http://koreabizwire.com/lg-uplus-commercializes-worlds-first-puf-based-usim/201433
[2] Geoffrey A. Moore, 1991, Crossing the Chasm: Marketing and Selling High-Tech Products to Mainstream Customers, Harper Business Essentials
[3] D. J. Jeon, et al., “A Physical Unclonable Function with Bit Error Rate < 2.3×10-8 based on Contact Formation Probability without Error Correction Code,” IEEE J. Solid-State Circuits, vol. 55, No. 3, pp. 805-816, March 2020.
[4] Teddy Kyung Lee, “Via PUF Technology as a Root of Trust in IoT Supply Chain”, Global Semiconductor Alliance Forum Article, May 8, 2020.
[5] Teddy Kyung Lee, “CBDC Wallets and the Security Requirements”, Global Semiconductor Alliance Forum Article, April 2021.

About Teddy Kyung Lee | ktlee@ictk.com | www.ictk.com
Teddy Kyung Lee is an IoT security professional working on bringing security features to network components such as Serial to Ethernet, LoRa network, Smart IoT sensors, industrial IoT, and FIDO applications. He is recently interested in Hardware Root of Trust solutions using Physical Unclonable Function (PUF) technology extended from his career background in hardware SoC design.
Teddy received a Ph.D. and M.S. degrees in Electrical Engineering from the University of Texas at Austin, and a B.S. degree in Electronics Engineering from Seoul National University, Seoul, South Korea. He worked in IBM Research Lab, Austin, TX, and Sun Microsystems, Sunnyvale, CA, as a circuit designer in microprocessor designs. Thereafter he worked in Juniper Networks, Sunnyvale, CA, and then Altera Corporation, San Jose, CA as a methodology leader. Scouted as an overseas brain by the Korean government, he worked in the development of security SoC for IoT applications. Recently, Teddy has been selected by the government as a Brain Pool scientist working on the development of a low power Post-Quantum PUF security SoC chip with an eSIM function embedded.
